All-in-one Security, Backup & Performance Solution for all your web assets
WebProtect is designed to make your Websites, Ecommerce, Apps, and SaaS Services Secure, Private, Fast, and Reliable
All Plans Include
- Web Application firewall (WAF)
- SSL Certificate
- DDoS Protection
- Content Delivery Network (CDN)
- Anycast DNS
- Vulnerability/PCI Scans
- Monitoring & Alerting
- Reporting
- 24/7 Technical Support
Business
Suitable for websites requiring security & high performance

Loading...

Loading...
Professional
Ideal for Ecommerce, High-traffic Websites, Web & Mobile Applications

Loading...

Loading...
Enterprise
Perfect for Internet Applications with custom configurations and SLAs
Website Firewall (WAF)
Cloud-based WAF that actively blocks malicious traffic.
Custom WAF Rules
Tailor the WAF settings to safeguard your particular application or website against cyber
threats. Based on your specified parameters, implement actions such as blocking or prompting verification for incoming requests.
OWASP Core Ruleset
Automatically incorporates the OWASP ModSecurity Core Rule Set to defend against the primary
vulnerabilities identified by the Open Web Application Security Project (OWASP).
Page Rules
Page Rules allow you to customize page / url functionality to match your unique needs.
Bot Mitigation
Secure your web forms and APIs against programmatic attacks. With Bot Manager high performance
bot rules use browser validation to detect malicious automated traffic and prevent it from reaching your web application.
Rate Limiting (IP-based)
Limit the number of requests a certain IP address can make, and prevent abuse from "repeat
offender" IP addresses.
IPv6, HTTP/2, SPDY
Support both IPv4 and IPv6 connections to your site without a single change to your existing
infrastructure. HTTP/2 brings advancements in efficiency, security, and speed, particularly on high-latency and mobile connections.
Header Rewrites
Rewrite headers helps to control header request and response.
Comment Spam Protection
Stop spammers from posting to your website.
Content Scraping Protection
Protect all of your content including text, images and email addresses from web scrapers.
Captcha/JS Challenge
Captcha served to visitors matching the triggered rules, and JS Challenge will run a JavaScript
challenge that validates whether the visitor is using a legitimate browser.
SSL Certificate
WebProtect provides you with default SSL and allows updating with your existing purchased SSL
Custom SSL Certificate
Customers can deploy their own SSL certificates for terminating SSL/TLS at the edge.
L3/L4 DDoS Protection
Protection against L3/L4 (network and transport layers of OSI model) distributed denial of
service (DDoS) attacks.
CDN
Data centers located across the globe provide visitors with location-based access to your
website, while removing latency and improving performance.
Cache TTL Expiry
Cache time before data is fetched from origin.
Load Balancing
Traffic splitting rules enable the distribution of site traffic among alternative origins.
Geo Based Load Balancing
Global Load Balancing ensures that visitors receive dynamic content from origin servers
closest to them.
Anycast DNS
Fast responsive times globally and nearinstant updates.
Malware Monitoring
Protect your brand’s reputation by knowing when your site is blocklisted and remove the
headache of getting it removed.
Security Vulnerbility/PCI Scans
Vulnerbility Scanning for over 1000 plus security checks.
Reporting
Intuitive dashboard with different reporting options.
Alerting
Configure alerts to be received by email on different conditions.
Standard Support
24*7 Support Availability, Multiple Support Channels, Unlimited Support Requests,Self Service Platform
Measured Response Time.
Malware Remediation
One time professional Service.
Managed Service
Ongoing management with 24/7 Multi-channel Priority Support & Faster Response Time. Managed WAF,
CDN, DNS, SSL, Malware Monitoring etc.
Modern Web Security Challanges
- Has your website ever been attacked?
- Did you ever have to say ransom fees to retrieve data?
- Are your web assetts regulalary scanned for malware?
- Do you have backup of all your web assets?
96% of malware
is delivered via email, making it the most common attack vector
(Verizon, 2019)Use case
A company lost 1.65M Dirhams due to the SQL Injection happened to their eCommerce website
We have implemented Web Security Solution for their eCommerce websites which protected the website from attacks through http/s including SQL Injection, Cross Sripting etc.
Elevate your digital security with webProtect
where peace of mind meets cutting-edge protection
Fortified WebProtect Security
Protecting your website‘s security with a comprehensive approach, incorporating elements such as a Website Firewall (WAF), custom WAF rules, OWASP Core Ruleset, page rules, bot mitigation, rate limiting (IP-based), support for IPv6, HTTP/2, SPDY, header rewrites, comment spam protection, content scraping protection, Captcha/JS challenge, SSL certificate, custom SSL certificate, and L3/L4 DDoS protection ensures robust defense against a wide range of threats.
Boosting WebProtect Performance
Enhance your website‘s performance with webProtect‘s advanced CDN capabilities, including optimized cache TTL expiry, load balancing for efficient resource distribution, geo-based load balancing for targeted content delivery, and Anycast DNS for lightning-fast response times across the globe.
WebProtect‘s Monitoring & Analytics Suite
Elevate your webProtect experience with comprehensive Monitoring & Analytics, featuring advanced capabilities such as continuous Malware Monitoring, thorough Security Vulnerability/PCI Scans, detailed Reporting, and real-time Alerting, ensuring proactive security and actionable insights for your online presence.
Enhancing WebProtect Support & Services
Benefit from top-tier Support & Services with webProtect, offering comprehensive Malware Remediation and expert Managed Service solutions, ensuring proactive protection and seamless management of your online security needs.
Web Application Firewal (WAF)
A Web Application Firewall (WAF) is a security tool that protects web applications from various cyber threats by monitoring and filtering incoming and outgoing traffic
SSL Certificate
An SSL Certificate is a digital certificate that encrypts communication between a user‘s browser and a website, ensuring secure transmission of sensitive information
DDoS Protection
DDoS Protection safeguards websites and networks by mitigating and deflecting distributed denial-of-service attacks, ensuring uninterrupted online availability
Content delivery network (CDN)
A Content Delivery Network (CDN) is a distributed network of servers that accelerates the delivery of web content to users, improving website performance and reliability
Load Balancing
Load Balancing optimizes resource distribution across servers to ensure efficient performance and prevent overloads, enhancing system reliability
Anycast DNS
Anycast DNS enhances website reliability and speed by routing user requests to the nearest server location, minimizing latency
Malware Monitoring
Malware Monitoring ensures constant surveillance for malicious software, safeguarding systems from potential threats
Vulnerbility/PCI Scans
Vulnerability/PCI Scans identify weaknesses and ensure compliance with Payment Card Industry standards, enhancing overall security
Plan Includes
- Automatic Daily Website Backups
- Fast, reliable & easy one-click Restore
- Built-in daily Malware Scanning
- Continuous Security Monitoring
- 24/7 Technical Support
Modern Web Security Challanges
- Has your website ever been attacked?
- Did you ever have to say ransom fees to retrieve data?
- Are your web assetts regulalary scanned for malware?
- Do you have backup of all your web assets?
96% of malware
is delivered via email, making it the most common attack vector
(Verizon, 2019)Use case
A company lost 1.65M Dirhams due to the SQL Injection happened to their eCommerce website
We have implemented Web Security Solution for their eCommerce websites which protected the website from attacks through http/s including SQL Injection, Cross Sripting etc.
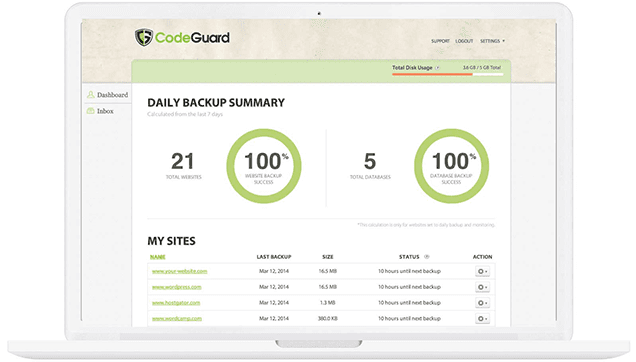
Website Backup that delivers 100% peace-of-mind
Utilizing sophisticated version control software, we provide incremental agent-less backups and 1-click restore option to reverse damage caused to your network of websites – with any mix of CMSs: WordPress, Joomla, Drupal – all in one place
With essential backup, malware remediation, and rollback capabilities we keep your site safe and secure
Daily Backup
Your website is auto backed up everyday and it only saves changes or updates to your storage space
Malware Protection
System automatically scans, discovers, and fixes viruses, trojans, rootkits, spyware, or other malware threats your website encounters
WordPress Plugin
For WordPress websites we provide the ability to manage backups, plugins and themes from a single dashboard. Users can even restore their website directly from the WordPress dashboard
Alerts & Notifications
Built-in technology that automatically sends you an email if there are any additions, modifications or deletions between each version of your website of what has been modified
Data Security
WebProtect adheres to industry best practices for data protection. All backups and passwords are encrypted, secure connections (SFTP/SSH/SSL) are used when possible, and annual vulnerability testing is performed by an independent agency. To date, WebProtect has not experienced any data breaches or successful hacks or attacks
Data Storage
Backups are stored on Amazon Web Services Simple Storage System, known as S3. S3 boasts object durability levels of 99.999999999%, achieved by storing redundant copies of data across multiple geographies and facilities. S3 is not the cheapest alternative for data storage, but it is one of the most reliable
Data Encryption
Our data stored on Amazon Web Services (AWS) is stored utilizing Server Side Encryption (SSE). AWS handles key management and key protection for us, with one of the strongest block ciphers available, 256-bit Advanced Encryption Standard (AES-256)
Database Backup
Yes, you can connect directly to your MySQL database, usually through Port 3306, or via SSH tunneling using either your FTP credentials or separate credentials. Each time we retrieve database content, a mysqldump command is executed. Most MySQL databases are small enough that this process does not create a noticeable server load

How does the Website Backup & Restoration work?
For the initial backup, all file content is retrieved using the “get” command over FTP or SFTP. This process utilizes disk I/O as each file is transferred to our servers, while CPU and memory requirements remain minimal
Subsequent backups are differential, meaning only the changed content is transferred. This is done using the “ls – list” command to examine file metadata, including name, size, timestamp, file type, permissions, and last modified date. If any of these attributes have changed or if a new file has been added, the modified or new file is transferred to our servers. If a file has been deleted, we update our repository accordingly. Because only the changed file content is transferred, the majority of subsequent backups require minimal memory, CPU, and I/O resources
When a customer requests to restore a previous version of their website, it first examines the live site to identify its current content. This allows us to efficiently sync the differences to or from your site. For example, if a hack alters only your .htaccess file, it will replace the compromised file with a clean, older version instead of reloading the entire site
You may also be interested in
We deliver best-in-class cybersecurity solutions for your organization's data, endpoint, web, email protection to prevent intrusions and stay resilient 3 product navigation under plan
10,000+ happy customers trust us
Frequently Asked Questions

Browse tips, article & how-to guides made for 24/7 Self-Help
Best Web Security, Backup & Performance solution for all your web assets in Middle East
Cloud Web Security in Dubai, Cloudflare Web Performance & Security in Abu Dhabi, Website Security & Performance in Al Ain, Webprotect in Ajman, Web Protection Services in Sharjah, Best Website Protection Service in Ras Al-Khaimah.Cloud Web Security in Riyadh, Cloudflare Web Performance & Security in Makkah, Website Security & Performance in Dammam, Webprotect in Madinah, Web Protection Services in Jeddah, Best Website Protection Service in Ras Al Khobar.
Cloud Web Security in Qatar, Cloudflare Web Performance & Security in Middle East, Website Security & Performance in Oman, Webprotect in Jordan, Web Protection Services in Egypt, Best Website Protection Service in Pakistan.
Cybersecurity threats force you to take action
Cybersecurity threats are a significant concern for any organization, and they often prompt actions to protect sensitive information and maintain business continuity. Here are some common actions organizations take in response to cybersecurity threats:
- Implement Strong Security Policies: Develop and enforce comprehensive security policies that address issues like password management, data encryption, and acceptable use.
- Regular Software Updates: Ensure all software, including operating systems and applications, are regularly updated to patch vulnerabilities and reduce the risk of exploitation.
- Conduct Security Training: Provide regular training to employees on recognizing phishing attempts, safe browsing practices, and secure handling of sensitive information.
- Deploy Security Tools: Use antivirus software, firewalls, intrusion detection systems, and other security tools to monitor and protect against malicious activities.
- Backup Data: Regularly back up important data and store backups securely, ensuring that you can recover information in case of a ransomware attack or other data loss incidents.
- Perform Risk Assessments: Conduct regular risk assessments to identify potential vulnerabilities and threats, and implement appropriate measures to mitigate them.
- Monitor Network Activity: Continuously monitor network traffic for unusual or suspicious behavior, which could indicate a security breach or attack.
- Implement Access Controls: Use role-based access controls to limit access to sensitive data and systems based on the needs of individual users.
- Incident Response Plan: Develop and regularly update an incident response plan that outlines procedures for responding to and recovering from a cybersecurity incident.
- Engage with Security Experts: Consult with cybersecurity experts or hire dedicated professionals to assess and improve your organization's security posture.
Taking proactive and reactive measures to address cybersecurity threats helps protect your organization's data, reputation, and overall operational integrity.
Take cybersecurity in your company to the next level
To elevate cybersecurity in your company, you should adopt a multi-layered approach that combines advanced technologies, processes, and strategies. Here are steps to take your cybersecurity to the next level:
- Adopt a Zero Trust Model: Implement a Zero Trust Architecture where no user or device is trusted by default, regardless of their location. Authenticate and authorize all access requests continuously.
- Enhance Threat Detection and Response: Invest in advanced threat detection solutions such as Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR) systems to quickly identify and respond to potential threats.
- Conduct Regular Penetration Testing: Regularly test your systems for vulnerabilities using ethical hackers or penetration testing services to identify and fix security weaknesses before malicious actors can exploit them.
- Strengthen Endpoint Security: Use advanced endpoint protection solutions that include threat intelligence, behavior analysis, and machine learning to safeguard devices against sophisticated attacks.
- Implement Multi-Factor Authentication (MFA): Require MFA for all critical systems and applications to add an extra layer of security beyond just passwords.
- Automate Security Processes: Leverage automation to streamline and enhance security operations, such as automated patch management, threat intelligence feeds, and incident response.
- Ensure Comprehensive Data Protection: Encrypt sensitive data both at rest and in transit. Implement data loss prevention (DLP) tools to monitor and control data movement within and outside the organization.
- Regular Security Audits: Perform comprehensive security audits and assessments regularly to ensure compliance with industry standards and identify areas for improvement.
- Develop and Test a Robust Incident Response Plan: Create a detailed incident response plan and conduct regular drills to ensure your team is prepared to handle and recover from cybersecurity incidents effectively.
- Enhance Security Awareness Programs: Go beyond basic training by incorporating ongoing awareness programs, simulated phishing exercises, and real-world attack scenarios to keep employees informed about emerging threats and best practices.
- Utilize Advanced Threat Intelligence: Integrate threat intelligence services to stay informed about the latest threats, vulnerabilities, and attack techniques relevant to your industry.
- Secure the Supply Chain: Assess and manage the cybersecurity posture of your suppliers and third-party vendors to ensure they adhere to security standards that protect your organization's data.
- Adopt Advanced Security Technologies: Explore emerging technologies such as artificial intelligence (AI) and machine learning (ML) to enhance threat detection, risk management, and automated response capabilities.
- Implement a Comprehensive Security Governance Framework: Develop a governance framework that includes clear roles and responsibilities, risk management policies, and regular reviews of security practices.
By taking these steps, you can significantly enhance your company’s cybersecurity posture and better protect against evolving threats.
what is the difference between internal cyber threats and external cyber threats
Internal and external cyber threats are two distinct categories of security risks, each with its own characteristics and potential impacts. Here’s a breakdown of the differences:
Internal Cyber Threats
Source:These threats originate from within the organization. They can come from employees, contractors, or other insiders who have access to the organization's systems and data.
Types:
- Malicious Insiders: Employees or contractors who intentionally cause harm, steal data, or sabotage systems.
- Unintentional Insiders: Employees who accidentally cause security breaches through negligence or lack of awareness (e.g., falling for phishing scams or mishandling sensitive data).
Motivation:
- Malicious Intent: Could be driven by personal grievances, financial gain, or espionage.
- Negligence or Mistake: Often results from a lack of training, awareness, or adherence to security policies.
Access: Insiders typically have authorized access to the organization’s systems and data, which can make detecting and mitigating their actions more challenging.
Detection and Prevention:
- Monitoring: Requires monitoring user activity, access controls, and behavioral analytics.
- Training: Ongoing security training and awareness programs can help mitigate unintentional threats.
External Cyber Threats
Source: These threats come from outside the organization and are typically carried out by cybercriminals, hackers, or adversarial entities with no legitimate access to the organization's systems.
Types:
- Cybercriminals: Individuals or groups seeking financial gain through activities such as ransomware attacks, phishing, or identity theft.
- Hacktivists: Groups or individuals motivated by political or social causes aiming to disrupt or expose information.
- Nation-State Actors: Government-sponsored entities involved in espionage, cyber warfare, or sabotage.
Motivation:
- Financial Gain: Such as through ransomware, data theft, or fraud.
- Political or Social Agendas: Aimed at advancing a particular cause or disrupting societal functions.
- Espionage: Gathering sensitive information for competitive or strategic advantage.
Access: External threats do not have authorized access and typically exploit vulnerabilities or weaknesses in systems to gain entry.
Detection and Prevention:
- Security Tools: Involves using firewalls, intrusion detection systems (IDS), and threat intelligence to identify and block attacks.
- Vulnerability Management: Regularly updating and patching systems to address known vulnerabilities.
In summary, internal threats come from within and can be intentional or accidental, while external threats originate outside the organization and often involve unauthorized attempts to compromise security. Both require different strategies and tools for detection, prevention, and response.
Why data backup is important in cyber security service
Data backup is a crucial component of a comprehensive cybersecurity strategy for several reasons:
Data Recovery from Attacks
- Ransomware: In the event of a ransomware attack, where data is encrypted by malicious actors, having up-to-date backups ensures that you can restore your data without paying the ransom.
- Malware: Backups help recover data if malware corrupts or deletes files.
Minimizing Downtime
Business Continuity: Quick access to backups allows for rapid recovery and minimizes operational downtime, helping to maintain business continuity during and after an attack.
Protection Against Human Error
- Accidental Deletion: Employees might accidentally delete important files or data. Backups allow for the restoration of accidentally lost or modified data.
- Incorrect Changes: Inaccurate changes or configuration errors can be rolled back with backups.
Mitigating Hardware Failures
Hardware Malfunctions: Hard drive crashes, server failures, or other hardware issues can result in data loss. Regular backups ensure that data is not permanently lost due to hardware failure.
Compliance and Legal Requirements
- Regulations: Many industries have regulations and standards that require data to be backed up regularly and securely. Compliance helps avoid legal penalties and maintains customer trust.
- Audit Trails: Backups can also provide an audit trail for data access and changes, which is useful for compliance and investigative purposes.
Protecting Against Data Corruption
File Corruption: Data files can become corrupted due to software bugs or hardware issues. Backups allow you to restore uncorrupted versions of your data.
Disaster Recovery
Natural Disasters: In the event of natural disasters such as fires, floods, or earthquakes, having offsite or cloud backups ensures that data can be recovered even if physical infrastructure is damaged or destroyed.
Long-Term Data Preservation
Historical Records: Backups provide a historical record of data, which can be valuable for auditing, analyzing trends, or recovering information that is no longer available through active systems.
Business Resilience
Risk Management: Regular backups are part of a broader risk management strategy, enhancing overall business resilience and preparedness for unforeseen events.
Best Practices for Data Backup
- Regular Backups: Schedule regular backups to ensure data is consistently up-to-date.
- Multiple Locations: Store backups in multiple locations, such as on-site, off-site, and in the cloud, to safeguard against various risks.
- Testing: Regularly test backups to ensure they can be restored effectively and verify their integrity.
- Encryption: Encrypt backups to protect data from unauthorized access during storage and transfer.
In summary, data backups are essential for recovering from data loss, ensuring business continuity, complying with regulations, and maintaining overall cybersecurity resilience.